تم سرقة مئات الآلاف من U، مما كشف عن العملية الكاملة لعملية احتيال جديدة على الأصول تستهدف لاعبي TG Bot
Original author: Box | 826.eth (X: @BoxMrChen )
Recently, more and more friends have come to me to tell me that their private keys have been stolen for no apparent reason. To be honest, I don鈥檛 believe it. However, after many investigations, we found that they actually have a very obvious characteristic, that they are all local players. After investigation and summary, we finally summarized a complete process chain. I hope it can be of some inspiration to everyone.
1. Automatically cast the net
As Sols ecosystem grows rapidly, there are now many automated monitoring robots that are very sophisticated and can obtain a large amount of information for analysis, and attackers are the first to take advantage of this.
Lets demonstrate this with an example.
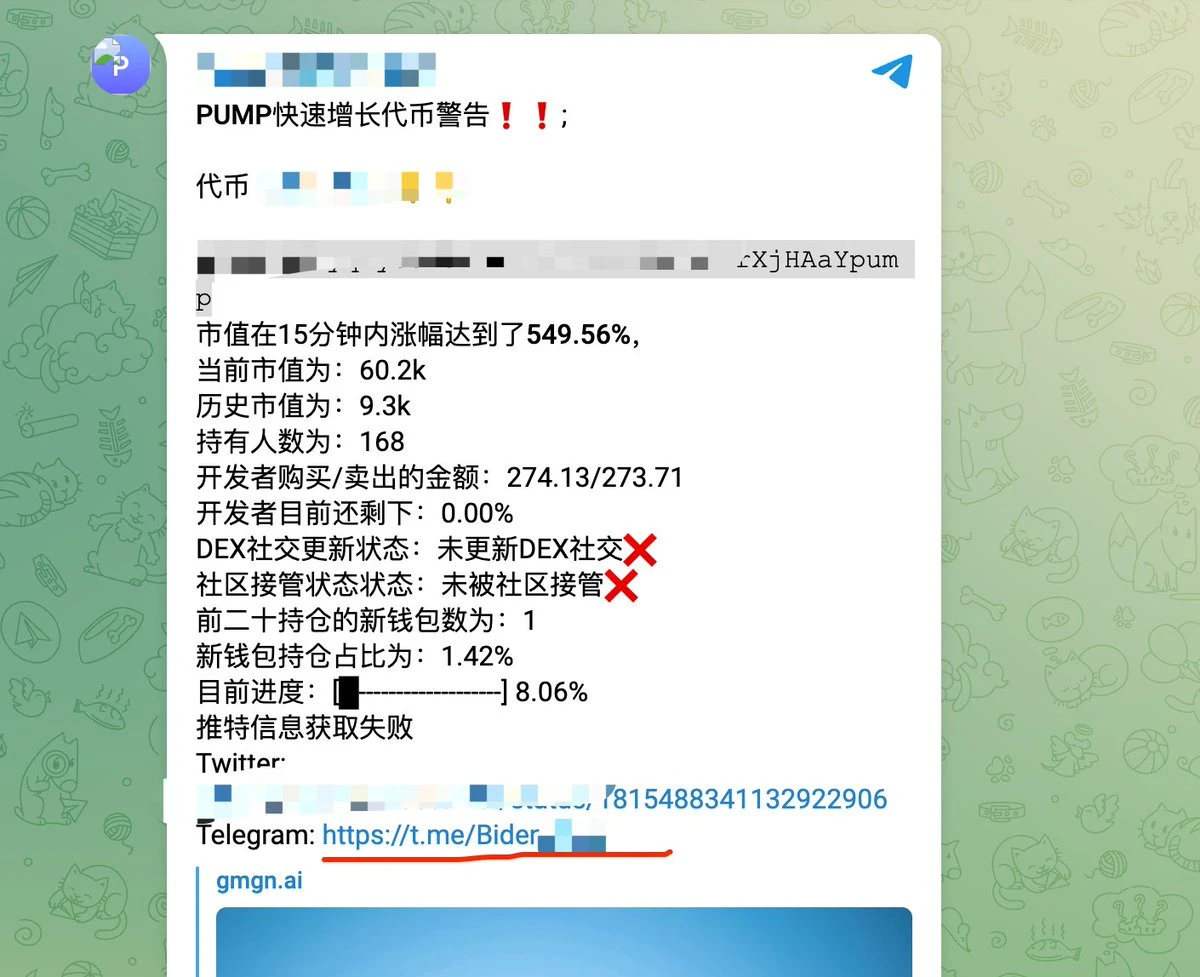
Pay attention to the place marked by the red line, where a Telegram group appears. This happens to be the main entrance to the theft.
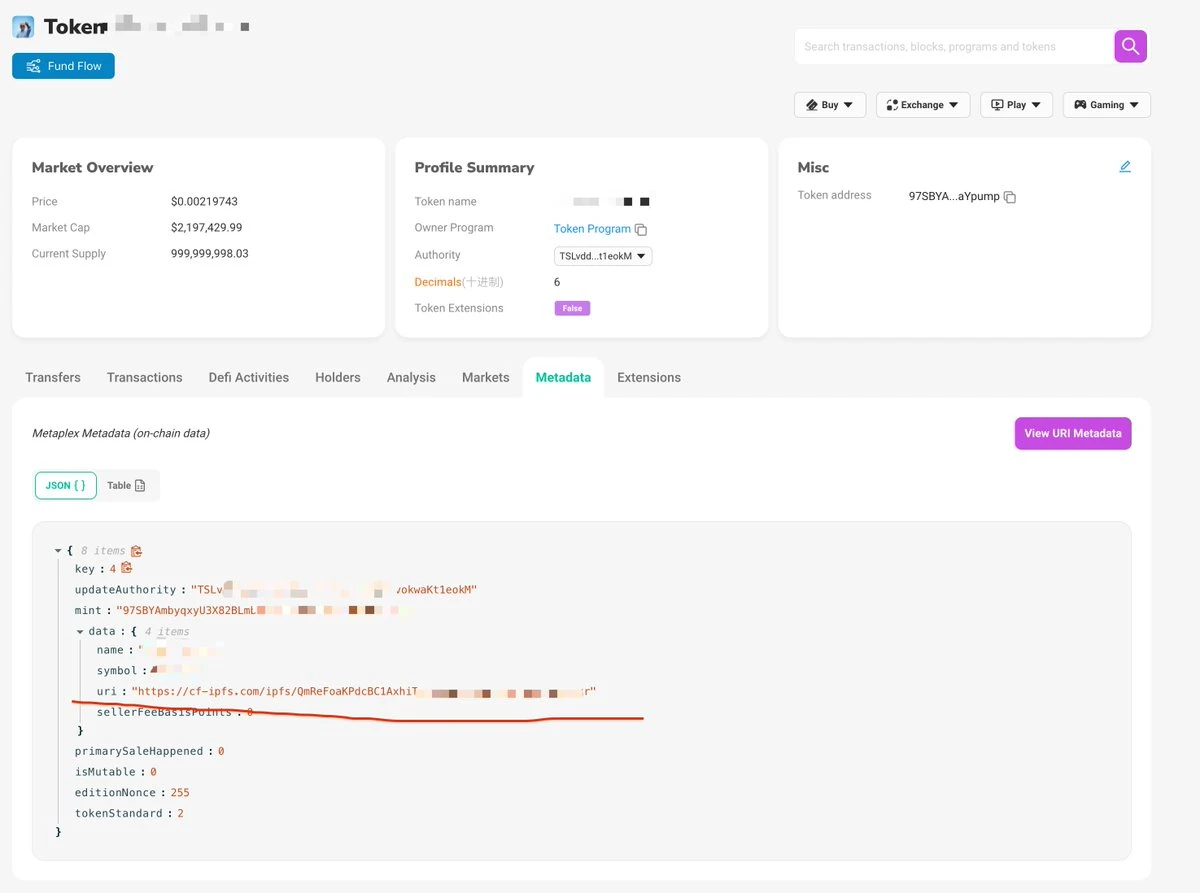
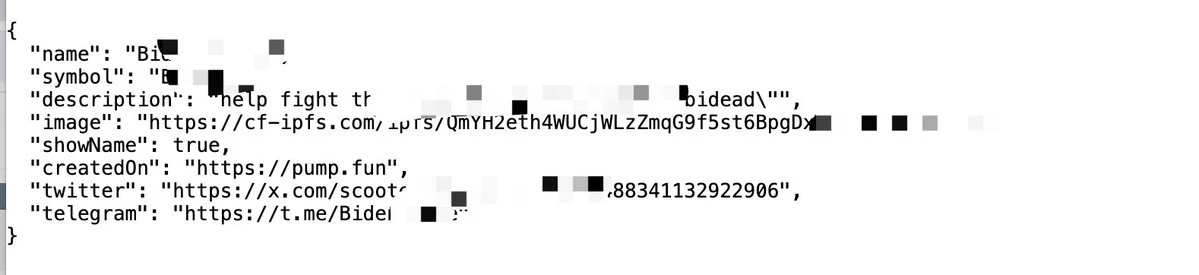
Sols tokens are quite unique. By uploading Metadata, a lot of data can be automatically set, such as avatars, social links, etc.
It can be seen that the data here is exactly the data displayed by the monitoring robot. In other words, the attackers took advantage of the highly credible channel that everyone believes in, such as the monitoring robot , to spread their phishing links.
To trigger this kind of monitoring, you only need to set up some robots to pull the market. They only need to make the data look good, and many people will be easily fooled. Now proceed to the next step.
2. False Verification
If you accidentally click on this TG and want to enter these TG groups, congratulations, you are one step closer to being stolen. Thanks to TGs latest mini-program function, attackers have a perfect way to make fakes look real. When you enter these groups, you will see a verification request, which is very common because many TG groups have to prevent robots, so it is also a very credible requirement. When you click on it, you need to be careful.
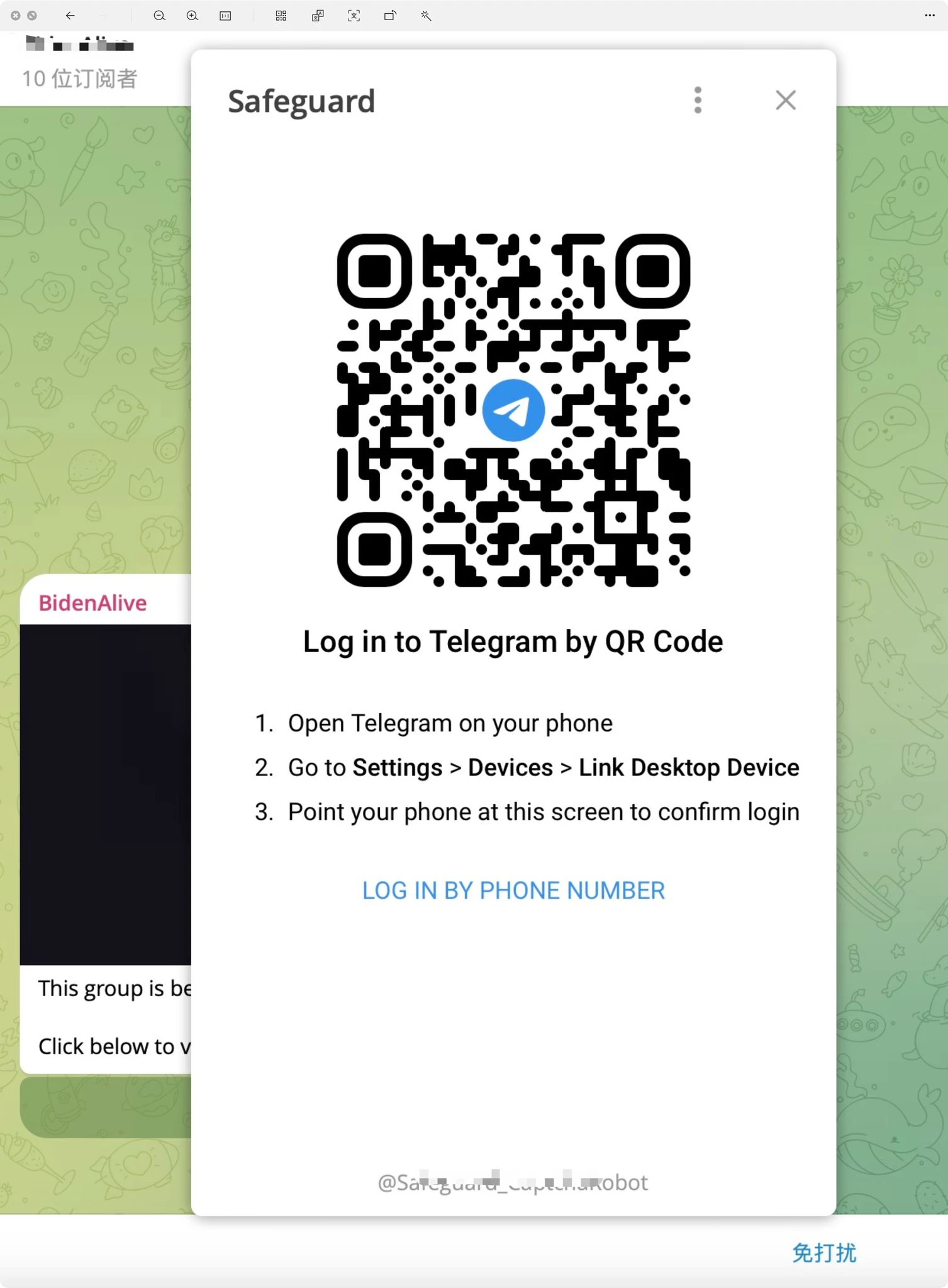 At this time, he will use the TG applet to pop up a realistic TG login window. If you accidentally scan the code at this time, Im sorry, your TG has been logged in and controlled by the attacker.
At this time, he will use the TG applet to pop up a realistic TG login window. If you accidentally scan the code at this time, Im sorry, your TG has been logged in and controlled by the attacker.
3. Record Scan
At this stage, the attacker will quickly scan your chat history and your various TG Bots. As we all know, the current TG Bots are basically naked, and the attacker can easily take your assets from your Bot. The target users they attack happen to be these local dog players, and the target users are clear. At this time, many high-value meme coins become the hackers meal.
At this point, the attack is over. Why is this case worth talking about? Because many users cant even tell that its a hacker attack. When they consult us, they wont provide any information about TG. They always believe that there is a computer Trojan or phishing link. The whole process seems very credible to ordinary users, from the credible monitoring bot to the credible TG verification, there is no suspicious operation in any part.
Rescue measures
After you scan the code, your information should be synchronized immediately. We recommend that you do the following.
1. Immediately transfer all the assets in the Bot, in order from large funds to small funds.
2. Check the devices that have logged in in TG and exit the suspicious devices immediately.
3. Contact TG regulars and declare that your TG account has been stolen to prevent further credible dissemination.
4. If you have assets that need to be rescued or sorted out, please contact @BoxMrChen , the professional team is trustworthy.
This article is sourced from the internet: Hundreds of thousands of U were stolen, revealing the whole process of a new asset fraud targeting TG Bot players
Related: Encourage Binance MVB, explain Blackwing protocol business and interaction methods
Original | Odaily Planet Daily ( @OdailyChina ) Author锝淣an Zhi ( @Assassin_Malvo ) Yesterday, BNB Chain announced the winners of the first BNB Incubation Alliance event jointly organized with Binance Labs. They are Payman , BalloonDogs , and Blackwing . These three projects will be admitted to Binance鈥檚 MVB program and receive funding from BNB Chain, as well as potential investment opportunities from Binance Labs . The first two projects are still in the early conceptual stage of the white paper, and the Blackwing white paper has clearly stated that there will be token airdrops , so Odaily will analyze the protocol and interactions of Blackwing in this article. Blackwing Interpretation Protocol Definition There are two official definitions of the Blackwing protocol, one is a modern DEX abstraction layer and…