原创 | Odaily星球日报( @OdailyChina )
作者:Azuma( @azuma_eth )
At around 11 pm Beijing time last night, the on-chain analysis agency Lookonchain detected an abnormal transaction. After a certain address (0xA7A1c66168cC0b5fC78721157F513c89697Df10D) received about 1.67 million EIGEN from the Eigenlayer team address, it directly sold them all at a price of US$3.3, cashing out about US$5.51 million.

After the transaction was exposed, doubts arose within the community – EIGEN had just lifted the transfer restrictions a few days ago, and the team was so blatant as to dump the market?
At around 5:30 this morning, EigenLayer gave an official response to community questions.
In an isolated incident this morning, an investors email about transferring tokens to a custody address was hijacked by a malicious attacker, who replaced the specific address in the email, resulting in 1,673,645 EIGEN being mistakenly transferred to the attackers address. The attacker has sold the stolen EIGEN through decentralized trading platforms and transferred the stablecoins to centralized exchanges. We are in contact with these platforms and law enforcement. Some funds have been frozen.
The breach did not affect the Eigenlayer system, there are no known vulnerabilities in the protocol or token contracts, and the incident is not related to any on-chain functionality of EigenLayer.
We are still investigating this situation and will continue to disclose further information as it becomes available.
The attack itself is not complicated. Yu Xian , a well-known security expert and founder of SlowMist, gave a very detailed analysis on his personal X.
Regarding the attack itself, the attacker may have planned it for a long time. The attackers address first received 1 EIGEN, and after about 26 hours, it received 1673644 EIGEN, all from the 3/5 multi-signature address (0x87787389BB2Eb2EC8Fe4aA6a2e33D671d925A60f). Then, more than an hour later, various coin laundering began. Gas came from ChangeNow, and the illegally obtained EIGEN was mainly exchanged for USDC/USDT, and mainly laundered through platforms such as HitBTC.
The official reason for the attacker’s success was that the email was hacked. It is estimated that in the email content, the wallet address that was supposed to receive EIGEN was replaced with the attacker’s address, causing the project party to send EIGEN to the attacker’s address. Even if 1 EIGEN was sent first, the attacker might have sent 1 EIGEN to the expected receiving address after receiving 1 EIGEN, causing the expected recipient to think that the entire process was correct… Of course, this is just speculation, and the specific details are subject to official disclosure.
However, this ordinary security incident exposed another more serious problem – why can EigenLayer investors receive EIGEN tokens now? And why can the receiving address (whether it is an investor or a hacker) sell EIGEN directly without restrictions after receiving it?
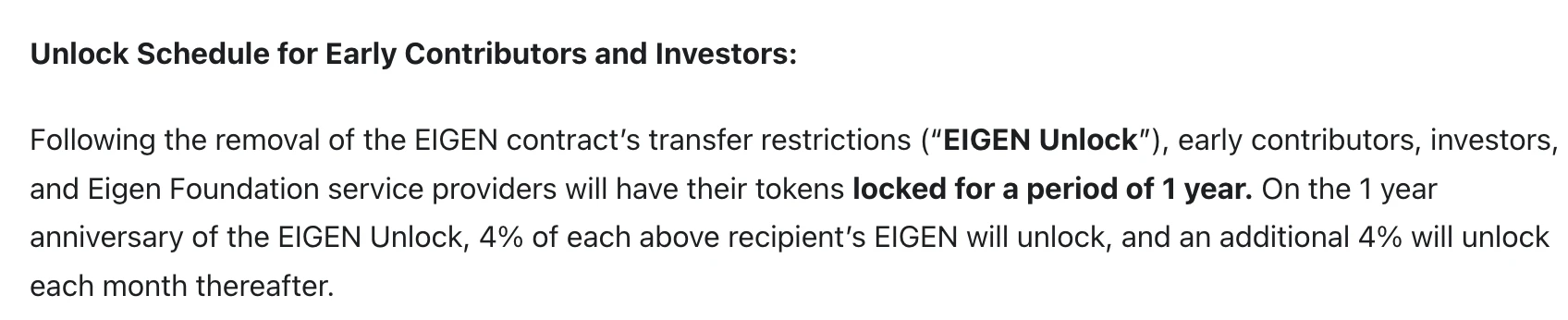
In the token economic model previously disclosed by EigenLayer, the portion regarding the shares of early contributors and investors clearly emphasized the 1-year lock-up limit in black and white .
After the transfer restrictions on the EIGEN contract are removed, the tokens of early contributors, investors, and Eigen Foundation service providers will be locked for one year. After one year, 4% of the EIGEN of each of the above recipients will be unlocked, and an additional 4% will be unlocked every month thereafter.
As a king-level project with a financing scale of over 100 million, a TVL ranking high in the entire ecosystem, and all major exchanges are competing to launch it… It is hard to imagine that EigenLayer neither chose to use the current mature token distribution protocol nor deployed a token unlocking contract by itself, but rather brainlessly sent tokens to the investors address immediately after the transfer restriction of the token was lifted …
Judging from the hacker’s selling behavior, these addresses were not subject to any rigid operation restrictions after receiving the tokens. In other words, EigenLayer seems to be counting on VCs to “morally lock up”…
What’s even more outrageous is that after EigenLayer received an email from an “investor” (actually a hacker) about changing the address, it did not cross-confirm through a phone call or other means , but directly released the money and coins, which led to the hacker successfully stealing millions of dollars in funds…
All in all, this whole incident is full of flaws. If EigenLayer had followed the normal token unlocking regulations, and if the EigenLayer team had a slightly better operational quality, this hacking incident would not have happened, and EigenLayer would not have been criticized by the community as a grassroots team.
From a technical perspective, EigenLayers innovative re-staking narrative expands the boundaries of node verification services, using AVS to expand node verification services that were originally only used for network consensus maintenance to more niche scenarios such as oracles, sequencers, and cross-chain bridges. This has long-term utility significance for the Ethereum ecosystem and even the entire cryptocurrency market.
But technology is technology, and operations are operations. From the past controversy of team members asking for airdrops from ecological projects to the current unlocking storm, these outrageous operations of EigenLayer are gradually overdrawing the trust of the community. For any project, no matter how large it is, this is an extremely dangerous signal.
This article is sourced from the internet: A hacker incident accidentally revealed the veil of EigenLayer







