Se revela el robo de GCR: ¿Quién es el hacker? ¿Cuánto dinero ganó?
Original author: ZachXBT
Compilado por: Odaily Planet Daily Azuma
Editor’s note: This article is a data analysis by ZachXBT, a well-known on-chain detective, on the theft of the X account of legendary trader GCR last weekend.
Last weekend, GCRs X account (@GCRClassic) was stolen, and it published order-calling content about ORDI and ETHFI, causing the market of related currencies to fluctuate violently in the short term. ZachXBT found through on-chain analysis that the theft seemed to be related to the development team Sol (not related to the Solana team) of the meme token CAT on Solana.
The following is the original content of ZachXBT, translated by Odaily Planet Daily.
This article is an analysis of the connection between the CAT development team Sol and the GCR theft incident.
Minutes before the hack, an address associated with the “Sol” team opened a $2.3 million ORDI and $1 million ETHFI long position on Hyperliquid.
Let’s start uncovering the secrets.
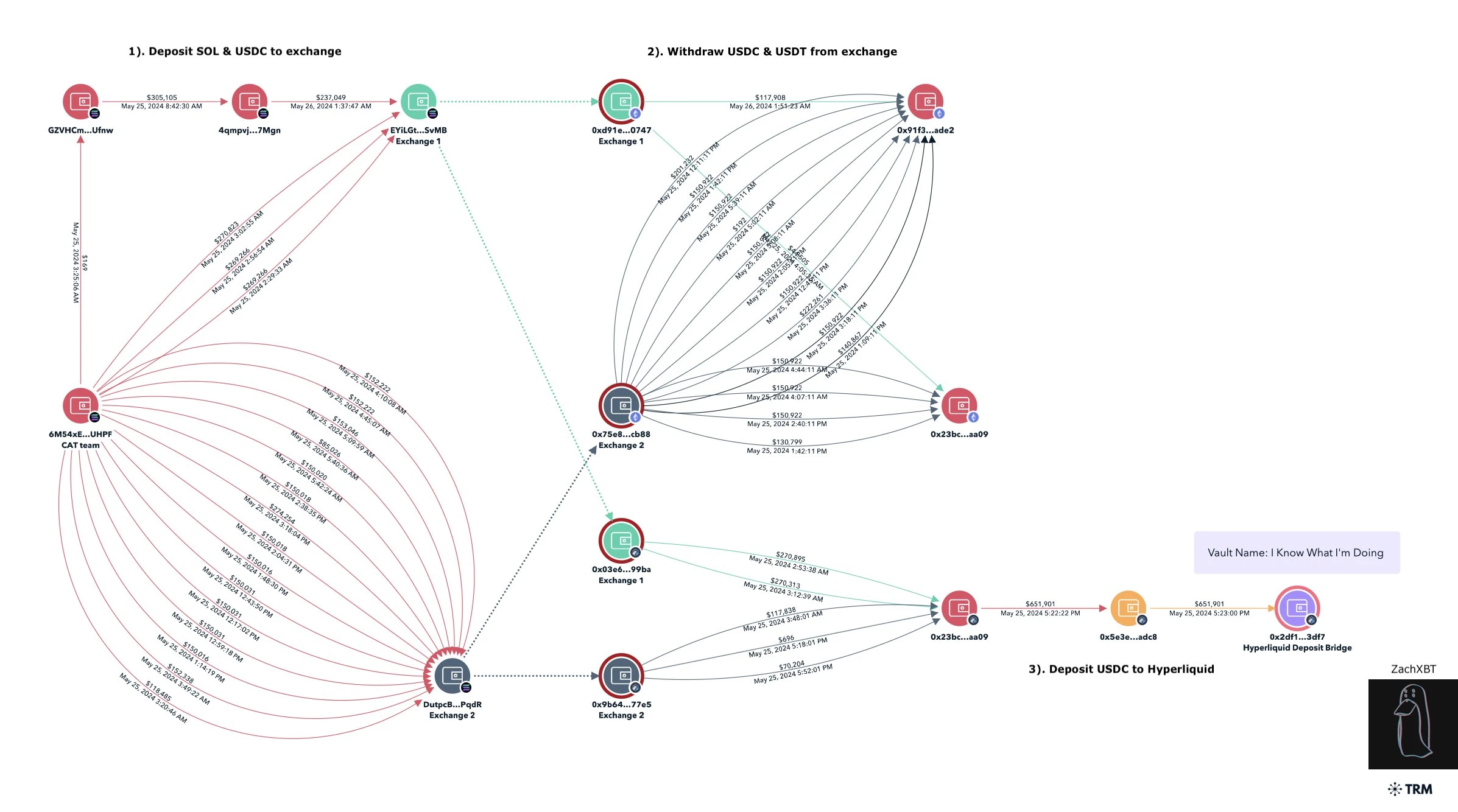
The on-chain analysis service Lookonchain has monitored and pointed out that the Sol team was suspected of sniping the meme token CAT issued by itself, controlling 63% of the token supply. It has now sold it for more than 5 million US dollars, and the profits have been dispersed and transferred to multiple addresses.
Among them, the address starting with 6M54x (6M54xEUamVAQVWPzThWnCtGZ7qznomtbHTqSaMEsUHPF) received about 15,000 SOL (worth about 2.5 million US dollars), and began to deposit funds to Kucoin (about 4,800 SOL) and MEXC (about 4,800 SOL and 1.4 million US dollars) on May 25.
Based on time analysis, I found that shortly after the two deposit transactions on Solana were completed, two batches of withdrawal transactions on Kucoin and MEXC appeared on Ethereum and Arbitrum, and the withdrawal amounts were very similar to the deposit amounts. The relevant addresses are as follows:
-
0x23bcf31a74cbd9d0578bb59b481ab25e978caa09;
-
0x91f336fa52b834339f97bd0bc9ae2f3ad9beade2.
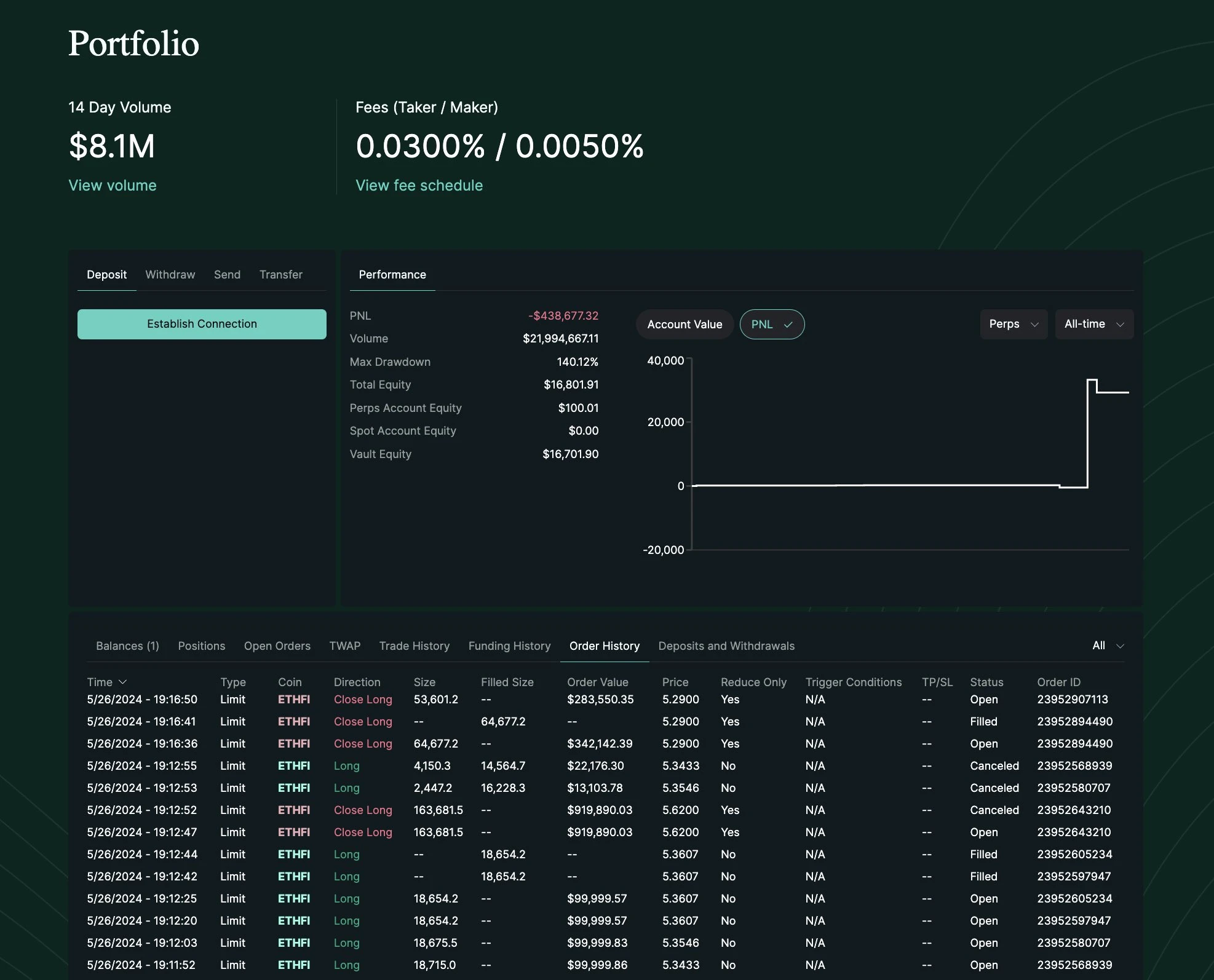
At 5:22 pm on May 25 (all UTC time), the above address starting with 0x 23 bc transferred $650,000 USDC to the address starting with 0x 5 e 3 (0x 5 e 3 edeb 4 e 88 aafcd 1 f 9 be 179 aa 6 ba 2c 87 cbbadc 8) and deposited it in Hyperliquid for contract trading. Subsequently , between 5:45 and 5:56 pm on May 26, the address starting with 0x 5 e 3 opened a long position of ORDI worth $2.3 million on Hyperliquid.
At 5:55 pm on May 26, GCRs X account posted a post about ORDI (bullish and heavily invested in ORDI), causing the price of ORDI to surge in the short term. The address starting with 0x5e3 then closed its position between 5:56 pm and 6:00 pm, making a profit of approximately $34,000.
At 5:58 pm on May 26, GCR posted a message on his other X account to confirm that his main account had been stolen.
Between 7:04 and 7:12 p.m. on May 26, the hacker repeated his old tricks. The address starting with 0x5e3 first opened a $1 million long position in ETHFI on Hyperliquid. Then at 7:12 p.m., the hacker used the stolen GCR account to post another order call about ETHFI.
However, this time the market seemed to have been alerted, and ETHFI did not replicate the trend of ORDI. Between 7:16 and 7:45 pm, the address starting with 0x5e3 was forced to close its position, resulting in a loss of approximately US$3,500.
The above is ZachXBT’s analysis of this hacking incident. From a data perspective, the hacker’s final profit from the two “manipulated transactions” was “only” about $30,000, and even one of them ended in a loss, which seems to be lower than many people’s guesses.
It is worth mentioning that since ZachXBT had previously warned the market about the suspected bad behavior of the Sol team, the CAT token community had ridiculed ZachXBT when the coin price rose short-term in the past two days (down 75% in the last 24 hours).
Now that he has found this opportunity, ZachXBT did not forget to make a sarcastic remark, and at the end of the article he specifically stated: From their strange operations, it can be seen that the hackers have extremely low IQ.
This article is sourced from the internet: GCR theft revealed: Who is the hacker? How much money did they make?
Relacionado: ¿Rebotes del manto (MNT)? Analizando el impacto de una venta de $36 millones
En resumen, el precio del manto marcó un nuevo máximo histórico esta semana, alcanzando $1.31 antes de corregirse ligeramente. Las ballenas vendieron alrededor de 30 millones de MNT en el lapso de tres días, lo cual era un resultado esperado. Las direcciones activas por rentabilidad muestran que menos de 12% de los participantes obtienen ganancias, lo que sugiere que es poco probable que se sigan vendiendo. El precio de Mantle (MNT) continúa impresionando a los inversores con sus aumentos y repuntes, lo que ha resultado en que la altcoin marque un nuevo máximo histórico. La pregunta ahora es si los poseedores de MNT pueden sostener este repunte o pasar a vender tokens. Los inversores de Mantle se mueven rápidamente El precio de Mantle alcanzó un máximo de $1.31 la semana pasada antes de corregirse para cotizar a $1.22 al momento de escribir este artículo. La altcoin todavía admite la media móvil exponencial (EMA) de 50 días. Sin embargo, como…